Cybersecurity in the Age of AI-Driven Attacks
Artificial Intelligence is transforming cybersecurity—but not just on the defensive side. Attackers are now leveraging AI to automate, scale, and personalize cyberattacks at unprecedented speed. As a result, we are entering a new phase of digital conflict: AI vs AI.
🚨 A New Era of Cyber Threats
Traditionally, cyberattacks required manual effort—crafting phishing emails, probing networks, or writing malware line by line. Today, AI tools can:
Generate highly convincing phishing emails in seconds
Automatically scan millions of systems for vulnerabilities
Modify malware code to evade detection
Learn from failed attacks and adapt instantly
This means attacks are becoming:
More targeted
Harder to detect
Faster to execute
More scalable
Organizations are responding with AI-powered security platforms from companies like Palo Alto Networks and CrowdStrike, which use machine learning to detect patterns invisible to traditional systems.
🤖 AI vs AI: The Cyber Arms Race
The cybersecurity battlefield is now driven by competing algorithms. Let’s break down how this works:
1️⃣ AI-Generated Phishing Emails
AI can analyze LinkedIn profiles, company websites, and social media posts to create hyper-personalized phishing emails.
Unlike old spam emails full of grammar mistakes, modern AI-generated messages:
Mimic tone and writing style
Reference real projects or colleagues
Use correct branding and formatting
This dramatically increases the success rate of phishing campaigns.
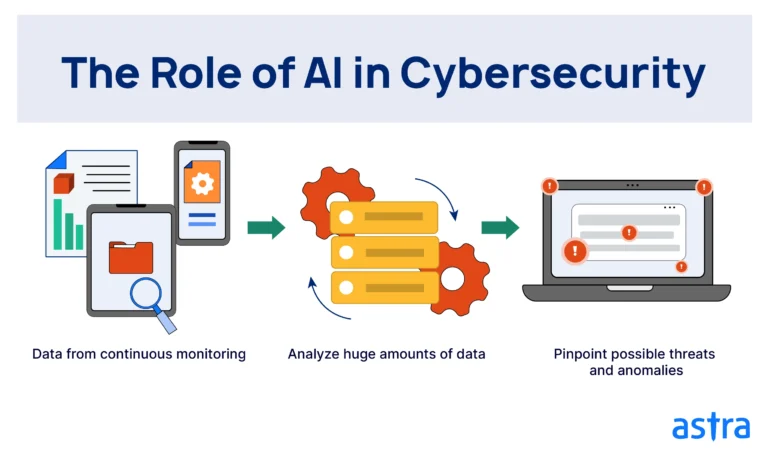
2️⃣ Automated Attack Detection
Defensive AI systems monitor:
Network traffic patterns
User behavior
Login anomalies
File access patterns
If an unusual behavior occurs—such as a login from a new country or abnormal data transfer—the system flags it instantly.
This is known as behavior-based threat detection, far more powerful than signature-based detection.
3️⃣ Behavioral Threat Analysis
Modern cybersecurity platforms analyze how users behave:
Typing speed
Mouse movement patterns
Device fingerprinting
Access timing habits
If behavior deviates from the normal pattern, AI triggers alerts—even if login credentials are correct.
This helps detect:
Insider threats
Compromised accounts
Account takeovers
4️⃣ Zero-Day Vulnerability Prediction
Zero-day vulnerabilities are unknown software flaws that hackers exploit before patches exist.
AI can:
Predict weak code patterns
Simulate attack scenarios
Detect anomalies in software behavior
By proactively identifying weaknesses, organizations can patch systems before attackers exploit them.
🏢 What Businesses Must Do
The rise of AI-driven threats requires a strategic shift.
✅ 1. Adopt AI-Based Security Platforms
Traditional firewalls are no longer enough. Businesses should implement:
AI-powered endpoint protection
Real-time threat intelligence
Automated response systems
Security must move from reactive to predictive.
✅ 2. Train Employees Continuously
Human error remains the weakest link.
Regular training should include:
Phishing simulation exercises
Social engineering awareness
Secure password practices
Multi-factor authentication adoption
AI can support—but humans must remain vigilant.
✅ 3. Secure Cloud and Edge Environments
With remote work and IoT expansion, security perimeters have dissolved.
Businesses must:
Implement Zero Trust architecture
Secure APIs and cloud storage
Monitor edge devices
Encrypt sensitive data
Every endpoint is now a potential entry point.
🌍 The Future of Cybersecurity
Cybersecurity is no longer just IT’s responsibility—it’s a business-critical function.
The future will include:
Autonomous AI security agents
Real-time global threat sharing
Self-healing networks
Quantum-resistant encryption
Organizations that embrace intelligent security today will remain resilient tomorrow.
🔎 Final Thoughts
We are witnessing the evolution of cyber warfare—from manual attacks to intelligent automation.

